By Ken Dilanian & Ted Bridis / The Associated Press
WASHINGTON—Hackers linked to China appear to have gained access to the sensitive background information submitted by intelligence and military personnel for security clearances, several US officials said on Friday, describing a second cyberbreach of federal records that could dramatically compound the potential damage.
The forms authorities believed to have been accessed, require applicants to fill out deeply personal information about mental illnesses, drug and alcohol use, past arrests and bankruptcies. They also require the listing of contacts and relatives, potentially exposing any foreign relatives of US intelligence employees to coercion. Both the applicant’s national identification number and that of his or her cohabitant is required.
The officials spoke on condition of anonymity because the security clearance material is classified.
In a news statement, the White House said that on June 8, investigators concluded there was “a high degree of confidence that…systems containing information related to the background investigations of current, former and prospective federal government employees, and those for whom a federal background investigation was conducted, may have been exfiltrated.”
“This tells the Chinese the identities of almost everybody who has got a United States security clearance,” said Joel Brenner, a former top US counterintelligence official. “That makes it very hard for any of those people to function as an intelligence officer. The database also tells the Chinese an enormous amount of information about almost everyone with a security clearance. That’s a gold mine. It helps you approach and recruit spies.”
The Office of Personnel Management (OPM), a central personnel database, which was the target of the hack, has not officially notified military or intelligence personnel whose security clearance data was breached, but news of the second hack was starting to circulate in both the Pentagon and the CIA.
The officials said they believe the hack into the security clearance database was separate from the breach of federal personnel data announced last week—a breach that is itself appearing far worse than first believed. It could not be learned whether the security database breach happened when an OPM contractor was hacked in 2013, an attack that was discovered last year. Members of Congress received classified briefings about that breach in September, but there was no mention of security clearance information being exposed.
The OPM had no immediate comment on Friday.
Nearly all of the millions of security clearance holders, including CIA, National Security Agency (NSA) and military special operations personnel, are potentially exposed in the security clearance breach, the officials said. More than 2.9 million people had been investigated for a security clearance as of October 2014, according to government records.
In the hack of standard personnel records announced last week, two people briefed on the investigation disclosed on Friday that as many as 14 million current and former civilian US government employees have had their information exposed to hackers, a far higher figure than the 4 million the Obama administration initially disclosed.
American officials have said that cybertheft originated in China and that they suspect espionage by the Chinese government, which has denied any involvement.
The newer estimate puts the number of compromised records between 9 million and 14 million going back to the 1980s, said one congressional official and one former US official, who spoke to the Associated Press on condition of anonymity because information disclosed in the confidential briefings includes classified details of the investigation.
There are about 2.6 million executive branch civilians, so the majority of the records exposed relate to former employees. Contractor information also has been stolen, officials said. The data in the hack revealed last week include the records of most federal civilian employees, though not members of Congress and their staffs, members of the military or staff of the intelligence agencies.
On Thursday a major union said it believes the hackers stole national identification numbers, military records and veterans’ status information, addresses, birth dates, job and pay histories; health insurance, life insurance and pension information; and age, gender and race data.
The personnel records would provide a foreign government an extraordinary road map to blackmail, impersonate or otherwise exploit federal employees in an effort to gain access to US secrets—or entry into government computer networks.
Outside experts were pointing to the breaches as a blistering indictment of the US government’s ability to secure its own data two years after a NSA contractor, Edward Snowden, was able to steal tens of thousands of the agency’s most sensitive documents.
The national identification numbers, known as Social Security numbers, were not encrypted, the American Federation of Government Employees said, calling that “an abysmal failure on the part of the agency to guard data that has been entrusted to it by the federal work force.”
OPM said it was increasing its use of encryption.
The Obama administration had acknowledged that up to 4.2 million current and former employees whose information resides in the OPM server are affected by the December cyberbreach, but it had been vague about exactly what was taken.
Former congressman Mike Rogers, the former chairman of the House Intelligence Committee, said last week that he believes China will use the recently stolen information for “the mother of all spear-phishing attacks.”
Spear-phishing is a technique under which hackers send emails designed to appear legitimate so that users open them and load spyware onto their networks.
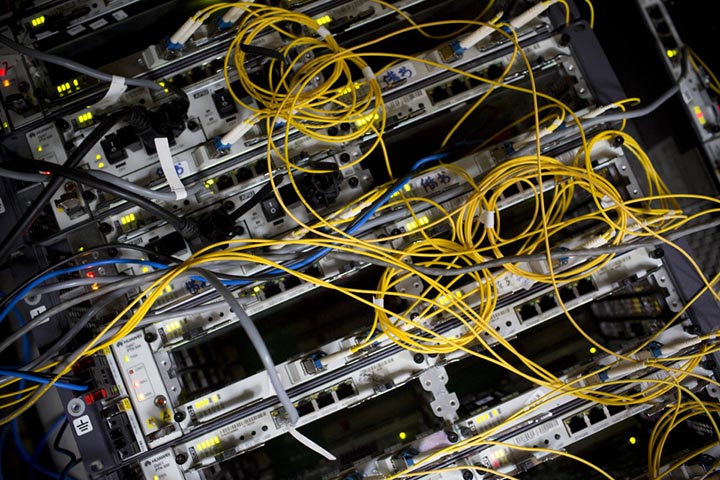
Image credits: AP/Susan Walsh